Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Development notes of CrackTheSurface
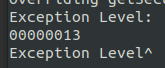
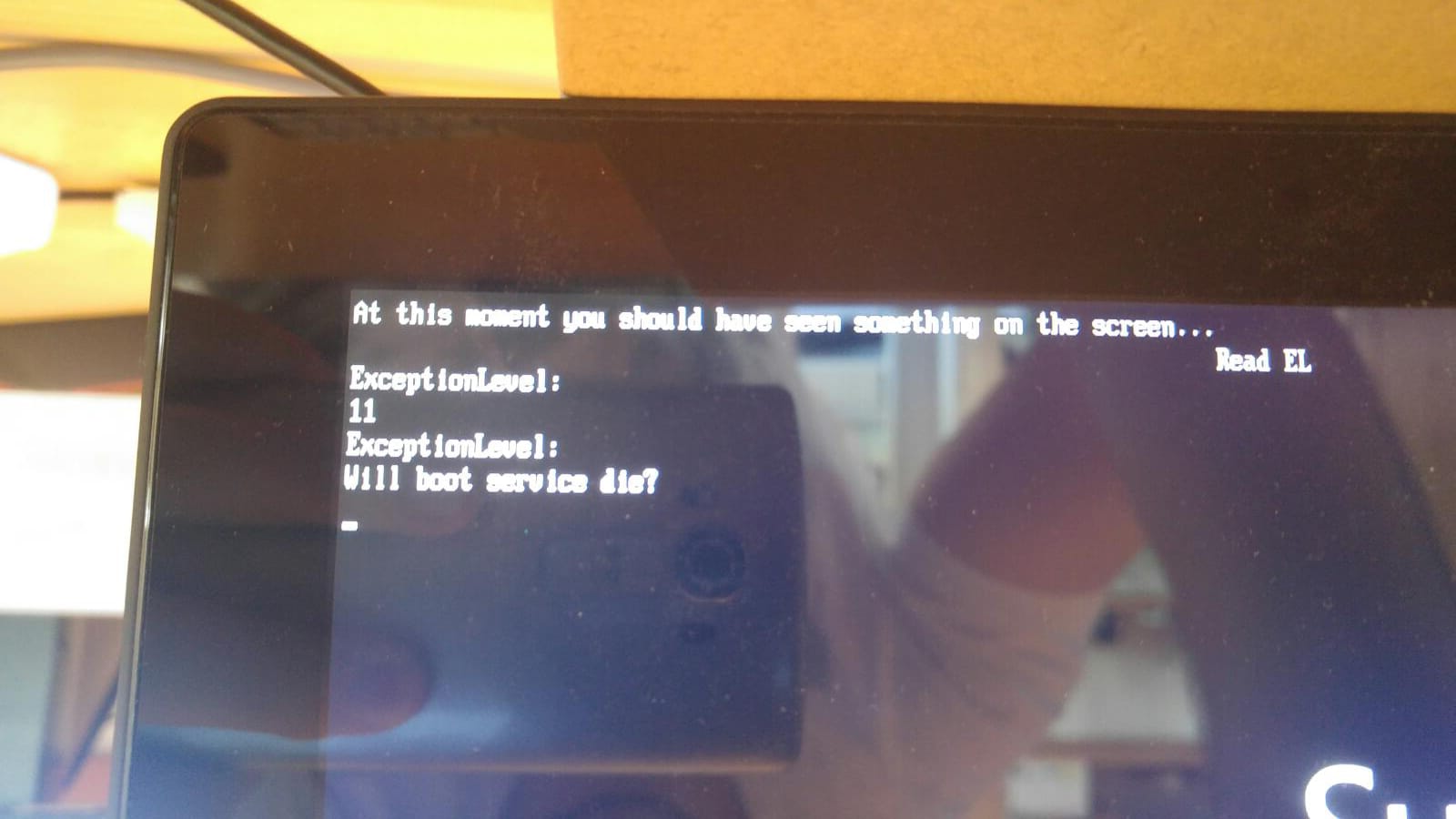
Write code into TZ mem and jump to it. Hopefully it will execute at EL3.
a custom payload will be used to read the Exception Level from in APX mode. I expect it to be 3.
Supervisor mode is the default mode to which a Supervisor Call exception is taken.
A normal efi App will be used to read the Execption Level from UEFI. I expect it to be 0.
FIQ mode is the default mode to which an FIQ interrupt is taken.
We need a relocateable payload since UEFI can give us different load addresses everytime.
Create payload which reads EL and reports back via serial. Read payload from USB/eMMC to memory. Disable TZ protection. copy payload into TZ mem. override TZ with jumps to payload address. If payload reads EL3 continue.
to be continued...
I2C0 @ 0x00 Address 0x00 is general call address which makes Cover incompatible with standard I2C drivers.
Address 0x00; Speed 400kHz
GPIO Interrupts: 0x59 -> L1 0x75 -> O5
From 5.1.1 HID Descriptor Format
All important information is set to 0x00. I guess standard I2C HID Driver will have a hard time.
HID Descriptor Address is 0x41. This makes all the Register fields seem legit.
It was tested without tCover. Connecting a tCover doesn't change anything.
This should be related to wrong power settings.
Surface RT2 turns on backlight on TypeCover2 when the kernel is booted from UEFI with ACPI.
ACPI does something right according to power settings. Now we need to capture the new HID Descriptor for UEFI boot on Surface RT. Results should show what to do next
Booting Windows without tCover: Windows doesn't send a single byte to tCover. Booting Windows with tCover: Windows does send some non HID bytes before the HID Descriptor is read.
That leads to the conclusion that the SoC has a GPIO which acts as tCover detector.
page 1697: can only be read from securemode.
page: 1139
Therefore we need to use Position independent code:
#define CPSR_M_SVC 0x13U |
#define CPSR_M_FIQ 0x11U |
Offset | Field | Size | Actual Value | Comment |
0 | wHIDDescLength | 2 | 00 1E | Dec: 30 -> 30 Bytes read |
2 | bcdVersion | 2 | 01 00 | Version 1.00 |
4 | wReportDescLength | 2 | 00 00 | x |
6 | wReportDescRegister | 2 | 00 42 | maybe |
8 | wInputRegister | 2 | 00 43 | maybe |
10 | wMaxInputLength | 2 | 00 00 | x |
12 | wOutputRegister | 2 | 00 44 | maybe |
14 | wMaxOutputLength | 2 | 00 00 | x |
16 | wCommandRegister | 2 | 00 45 | maybe |
18 | wDataRegister | 2 | 00 46 | maybe |
20 | wVendorID | 2 | 00 00 | x |
22 | wProuctID | 2 | 00 00 | x |
24 | wVersionID | 2 | 00 00 | x |
26 | RESERVED | 4 | 00 00 00 00 |
https://media.ccc.de/v/c4.openchaos.2018.06.glitching-the-switch dumping boot rom seems easy. only need to set the right access bits. which we can do since we have total control over the CPU/memory. Reverse engineering is the hard part. 48kB arm assembler. And only some bits decide from which device is booted from. But we have a good starting point. The provided example patches a function which prevents the bootrom to read the BCT. We need to patch some bits before this instruction is executed. and since reading the BCT is the first thing the bootrom does we should start looking at the begining of the function call chain. only need to figure out to which value we must set the byte. but this should also be easy. the bootdevice is read form a fuse. Nvidia provides a script to burn fuses. this should tell us which fuse is used for bootdevice selection and we should be able to find this address in the bootrom. it should also tell us which value the fusee needs to be to boot from mmc/sd/usb/... the theory part is "done". Need to dump the bootrom and throw the binary into ghidra. find the function which reads the boot device fuse and write an ipatch to patch the bootrom. like disableing security fuse. i hope this allows us to boot selfmade BCTs from other storage devices. luckily we dont have to do some voltage glitching. we could just set the bits to read the bootrom�
Secureboot registers should be located at 6000:c2000
https://phoenixnap.com/kb/how-to-resolve-merge-conflicts-in-git
git log --stat
Maybe we have to write a kenel module which will init the tCover IC and hand off controll to I2C-HID Driver